Download Openssh Backdoor Patch
Click to expand.How do i know. Get a mess in my servers (installing psybncS, eggdropS, and backdoorS in some unbeliveable locations like /var/spool/vbox, etc). So many unexpected connections i got from LogWatch (scanning, connection fail.etc) #3. They (i think they, not he/she) keep trying to search some cgi script (now i get a rid of a movetabletype cgi script that allow bypassing SSL/openSLL to the shell REF: h++p://www.webhostingtalk.com/showthread.php?threadid=120332&perpage=15&pagenumber=1) here is the story begin: - they get a cgi script (movetabletype; the script is mt.cgi) in one of my client public area. They execute some misc codes trough it so they got shell acc eventhough the user didn't or /bin/false. - they download/upload some compressed files (lately i know it is as Loadable Kernel Module tarball.
Ebury is a SSH rootkit/backdoor trojan for Linux and Unix-style operating. And the existing libkeyutils file is patched to link against this library instead of libc6. Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers.
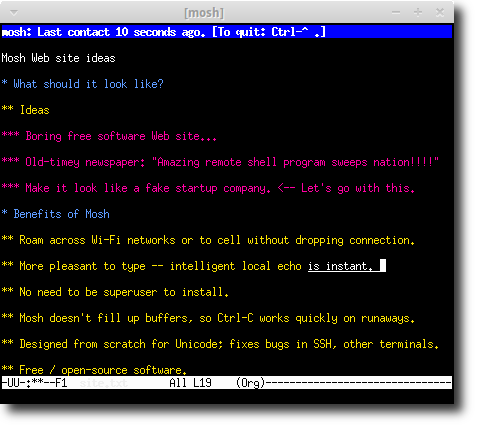
REF: securityfocus.com). - they install some backdoors (not just one) using unpredictable ports by infecting the openSSH 3.6.1p2 with backdoor patch REF: h++p://packetstormsecurity.nl/UNIX/patches/openssh-3.6.1p2-backdoor.patch.gz. - i've got so many notifications from sms-logwatch, LogWatch e-mail, and also by my eyes in the system. - i try to configure it. And here some of the result.
Try to upgrade the openSSH manually after there is no security update from cpanel. Result: FAIL (it need openSSL update) #2. Try to upgrade the openSSL. Result: WORK but some of my clients (using postnuke) complain about they site's session failed. Postnuke using old authentication method in it session scripts.
Now the servers is fresh by the name of RELOAD system that cost US$70 each. I'm suspending some accounts that infected by the intruders's misc scripts in they dirs. To be continuous I don't know. Guest wich one of the Open (SSL or SSH) get the title (bugs wash) now?! Or should i say the mod_ssl from the apache to? Click to expand.Yep. RH version is not vuln.
Did you know that openSSH in Linux box is a porting version from openSSH for openBSD version? Why cpanel choose it?
Why the old version (openssh.org)? CPanel don't choose to use a particular version, in as much as it is provided by RedHat. RedHat nearly always prefer to patch an old stable version with security patches, rather than release the latest version of an application which may be instable. Another good example is kernels - RedHat's are nearly always relatively old, but will security patches back-ported for stability reasons.
International 3444 backhoe manual. You can upgrade openssh if you want to, you just have to be careful when you do. Inceidentally, if you do a rpm -qi openssh you will probably see that openssh on RedHat Enterprise was rebuilt last in March 2004.
Not me but my host Dear Sir, I can see the problem is with openssh, but my host does not. They practically evicted my blog (using MT) from their server and as the reason the refer to this post here. They keep on saying 'the intrusion was caused by mt.cgi, see the post in cpanel forum'.
So please sir, can you elaborate more on how do you conclude that mt.cgi was the entry point? What Kind of 'misc code' that you refer above? I really like to use MT again but I don't want to be evicted again each time a webhoster read your post here. With crushed heart, Indonesian Hostless Blogger.
What is Open Secure Shell? Open Secure Shell (OpenSSH) is an open source version of the SSH protocol suite of network connectivity tools. The tools provide shell functions that are authenticated and encrypted. A shell is a command language interpreter that reads input from a command line string, stdin or a file. Why use OpenSSH? When you're running over unsecure public networks like the Internet, you can use the SSH command suite instead of the unsecure commands telnet, ftp, and r-commands. OpenSSH delivers code that communicates using SSH1 and SSH2 protocols.
What's the difference? The SSH2 protocol is a rewrite of SSH1. SSH2 contains separate, layered protocols, but SSH1 is one large set of code. SSH2 supports both RSA & DSA keys, but SSH1 supports only RSA, and SSH2 uses a strong crypto integrity check, where SSH1 uses a CRC-32 check. The Internet Engineering Task Force (IETF) maintains the secure shell standards.
OpenSSH has been updated to the 3.4p1 version of the open source code from openssh.org. You can download it from.
The primary new feature is user privilege separation, a security enhancement that prevents super user escalation risks by reducing the amount of code that runs with special privileges. User privilege separation is enabled by default in the OpenSSH server configuration file /etc/ssh/sshd_config: #UsePrivilegeSeparation yes The way it works is that a separate server process is created for each connection and when a request comes from a client, the ssh monitor process forks an unpriviledged child process that handles all of the requests from the client. If the client's request requires super user privileges the request is sent to the privileged monitor process. When you view the SSH processes started, you will see the sshd daemon for the monitor process and an unprivileged process owned by the client. For further detailed information about privilege separation, see the August 2002 article by Niels Provos,. Since AIX 5.2 is a new release of the AIX operating system, a separate compilation of the OpenSSH source code was completed on this level of the operating system.