Gmail Phishing Page Free
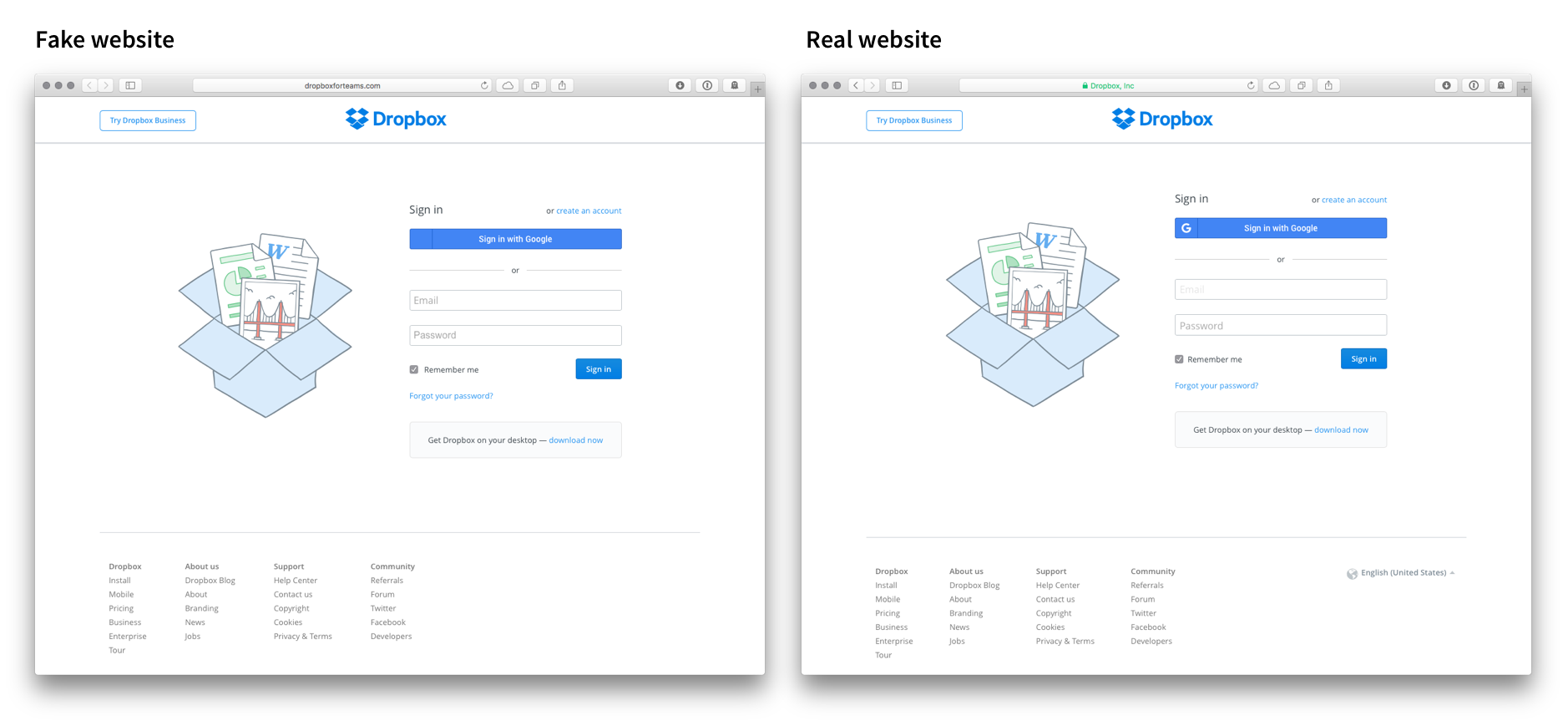
Phishing is another practical option you can use to hack Gmail. However, you should know that Phishing is not the easiest of tasks to perform. You should have to create a double of a certain website and trick the user.
Google Docs was pulled into a sneaky email phishing attack on Tuesday that was designed to trick users into giving up access to their Gmail accounts. The phishing emails, which circulated for about three hours before Google stopped them, invited the recipient to open what appeared to be a Google Doc. The teaser was a blue box that said, “Open in Docs.” In reality, the link led to a dummy app that asked users for permission to access their Gmail account. Reddit An example of the phishing email that circulated on Tuesday. Users might easily have been fooled, because the dummy app was actually named “Google Docs.” It also asked for access to Gmail through Google’s actual login service. The hackers were able to pull off the attack by abusing the OAuth protocol, a way for internet accounts at Google, Twitter, Facebook and other services to connect with third-party apps.

The OAuth protocol doesn’t transfer any password information, but instead uses special access tokens that can open account access. However, OAuth can be dangerous in the wrong hands. The hackers behind Tuesday’s attack appear to have built an actual third-party app that leveraged Google processes to gain account access. Reddit The dummy app will try to ask for account permission. “The attack is quite clever and it exploits the ability for you to link your Google Account to a third-party application,” said Mark Nunnikhoven, vice president of cloud research at security firm Trend Micro. Exploiting OAuth for account access is particularly devious because it can bypass the need to steal someone’s login credentials or even Google’s.
Last month, Trend Micro said a Russian hacking group known as Fancy Bear was using a that abused the OAuth protocol to phish victims. However, security experts said Tuesday’s phishing attack probably wasn’t from Fancy Bear, a shadowy group that many experts suspect works for the Russian government.
“I don’t believe they are behind this. Because this is way too widespread,” Jaime Blasco, chief scientist at security provider AlienVault, said in an email. On Tuesday, many users on Twitter, including journalists, screen shots of the phishing emails, prompting speculation that the hackers were harvesting victims’ contact lists to target more users.
The attack was also sent through an email address at “hhhhhhhhhhhhhhhh@mailinator. Com.” Mailinator, a provider of a free email service, any involvement. Fortunately, Google moved quickly to stop the phishing attacks, after a posted about them. “We’ve removed the fake pages, pushed updates through, and our abuse team is working to prevent this kind of spoofing from happening again,” Google said in a statement.
Security experts and Google recommend affected users check what third-party apps have permission to access their account and revoke any suspicious access. Users can do so by visiting this, or performing a Google. It’s also good practice to be careful around suspicious-looking emails. Many hacking attempts, including malware infections, come through links or attachments sent over email. Security firms are warning that other hackers may conduct similar phishing attacks abusing OAuth, not just through Google, but with Facebook and LinkedIn. “Like all other creative, novel approaches, it will likely be heavily copied almost immediately,” Cisco’s Talos security group in a blog post. Talos has identified more than 275,000 applications that use OAuth and connect to the cloud. Descargar xpadder 5.7 portable.